Data security doesn’t need to be a challenge!
Whether your data is stored within your database files or transmitted to your trading partners, using the right tools can mean the difference between meeting compliance and security best practices or suffering a data breach.

Townsend Security is well known for providing security solutions for a wide variety of platforms (IBM i (AS400, iSeries), IBM mainframe, VMware, Windows, Linux). Recently, our founder and CEO produced an excellent webinar on “Securing Your IBM i Using the Right Tools”. Many of our IBM i customers are under multiple compliance requirements including PCI, HIPAA, SOX, GLBA, and others which require securing data-at-rest and data-in-motion, real-time security event logging, file integrity monitoring, and two-factor authentication. The webinar covers encryption and key management as well as a number of our other auxiliary products specifically for the IBM i (AS400, iSeries) platform.
There were a number of excellent questions asked after the presentation, and the following is a brief recap of that Q&A session with links to additional information:
Q: Can I use FieldProc to protect multiple fields in a file?
A: The short answer is yes, encrypting multiple fields is a fully supported capability. FieldProc does allow, from both DB2 and from our solution, protecting multiple columns or fields in a DB2 file. You can define multiple fields and then enable FieldProc with one command on all those fields within our solution. People often ask if indexes can also be encrypted and yes, that is fully supported as well. There are a few limitations in legacy RPG applications, while with a native SQL application there are no limitations.
To learn more about Field Procedures on the IBM i, check out this blog: 5 Common FAQs About IBM i Encryption Using FIELDPROC
Q: Can’t I just transfer my file from IBM i to Windows and then PGP encrypt it there?
A: This is a great compliance question and comes up often with QSA Auditors. Yes, of course you can move a file from one machine to another using operations navigator. The problem is that it exposes data in the clear during the movement, either across the network if it is an unsecured connection or when the data lands on the other side of the transfer. Any of these exposures will likely result in an audit failure.
Good security practice, regardless of the platforms involved is:
- Encrypt at the Source
- Decrypt at the Destination
Make sure to securely move it in encrypted form and don’t let it get loose anywhere in between!
Learn more about the core components of a total encryption strategy in this blog: Secure Managed File Transfer and PGP Encryption
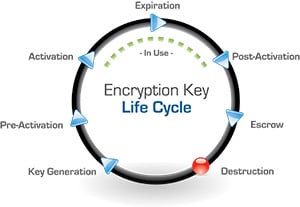
Q: How does key management work with older back-up copies of data that was secured with earlier keys?
A: Any Enterprise key management solution should maintain encryption keys under policy for as long as they are needed. As you generate new keys, the older keys are retained and made available for decryption purposes, until you retire those keys. Our solution will maintain multiple versions, and doesn’t have a limit on how many keys or generations you can have of master or key encryption keys. If you have a loss or need to delete data that is out of your control, you can then delete the key.
For more information on the full life cycle of keys, check out this blog: Why Key Management is So Critical in the Life Cycle of an Encryption Key
Q: Your two-factor authentication product is supported in which countries?
A: Since our 2FA solution is through TeleSign, a global company, it has a broad presence in more than 200 countries around the world and in 87 languages. By leveraging an individual's mobile phone, a reliable means of authentication has become readily available for the IBM i platform. For example, instead of tokens, businesses can simply send an SMS or voice message that contains a one-time authentication code to the individual user’s phone. This means cyber criminals cannot log into the IBM i without physical control of the actual phone.
This blog will outline Making a Case for Two Factor Authentication: Taking Security Beyond Usernames and Passwords