If you’ve been following this blog recently you know that I’ve been advocating for the use of encryption to help prevent ransomware attacks. Ransomware attackers have been adapting to the new reality that a lot of companies have deployed good backup strategies to recover their files. Without that leverage the attackers can’t extort payments for recovery of your systems.
So, what are they doing now? They are exfiltrating your sensitive data and using that as additional leverage.
 Oh, you have backups and you don’t want to pay? OK, we took your sensitive data and we are going to publish it. Do you have secret intellectual property or business plans? Do you have sensitive medical information on your patients? Do you have sensitive information about children in your care?
Oh, you have backups and you don’t want to pay? OK, we took your sensitive data and we are going to publish it. Do you have secret intellectual property or business plans? Do you have sensitive medical information on your patients? Do you have sensitive information about children in your care?
Under this kind of pressure many ransomware victims decide to pay the ransom.
That’s why it is important to encrypt your data before a ransomware attack. If the attacker can’t read your data because it is encrypted they can’t threaten to release it.
It has been frustrating to me that most security recommendations on how to protect yourself from a ransomware attack omit the step of encrypting your data first.
But that has now changed! And it is long overdue.
Here is what President Biden’s new executive order recommends (emphasis added):
What we urge you to do now:
Implement the five best practices from the President’s Executive Order:President Biden’s Improving the Nation’s Cybersecurity Executive Order is being implemented with speed and urgency across the Federal Government. We’re leading by example because these five best practices are high impact: multifactor authentication (because passwords alone are routinely compromised), endpoint detection & response (to hunt for malicious activity on a network and block it), encryption (so if data is stolen, it is unusable) and a skilled, empowered security team (to patch rapidly, and share and incorporate threat information in your defenses). These practices will significantly reduce the risk of a successful cyberattack.
And more ...
And this:
For Federal Agencies:
Modernize and Implement Stronger Cybersecurity Standards in the Federal Government. The Executive Order helps move the Federal government to secure cloud services and a zero-trust architecture, and mandates deployment of multifactor authentication and encryption within a specific time period. Outdated security models and unencrypted data have led to compromises of systems in the public and private sectors. The Federal government must lead the way and increase its adoption of security best practices, including by employing a zero-trust security model, accelerating movement to secure cloud services, and consistently deploying foundational security tools such as multifactor authentication and encryption.
Encryption is not the only thing you need to do, but it is a critical part of a ransomware protection strategy. It is heartening to see this being recognized.
There is some good news: Encryption is fast, easy and affordable. If you are a small or midsize organization you will be glad to know that there is an affordable solution for your encryption strategy. Encryption and encryption key management are no longer the headaches they once were. You or your IT Support organization can address your encryption needs in a rapid manner.
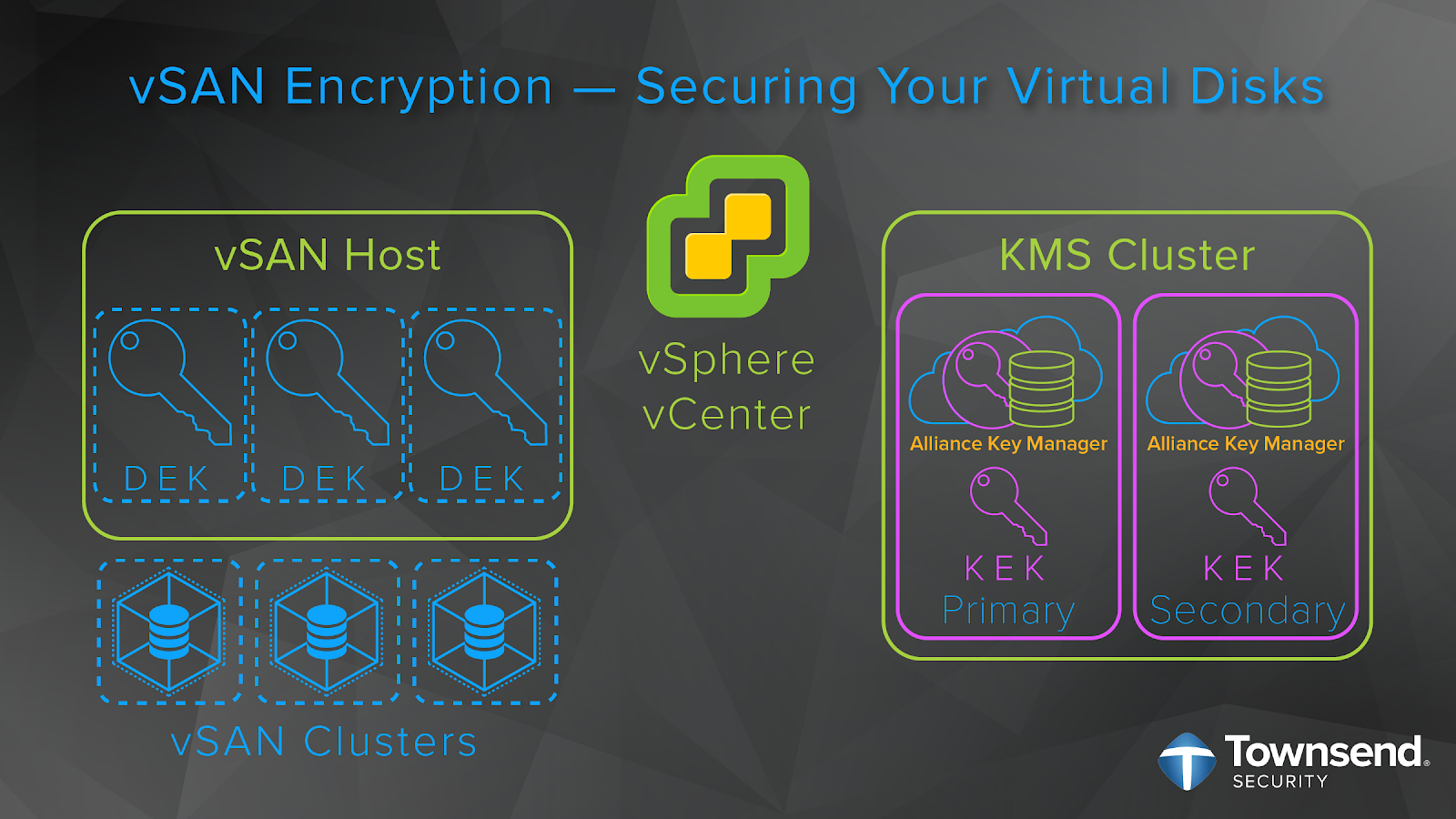
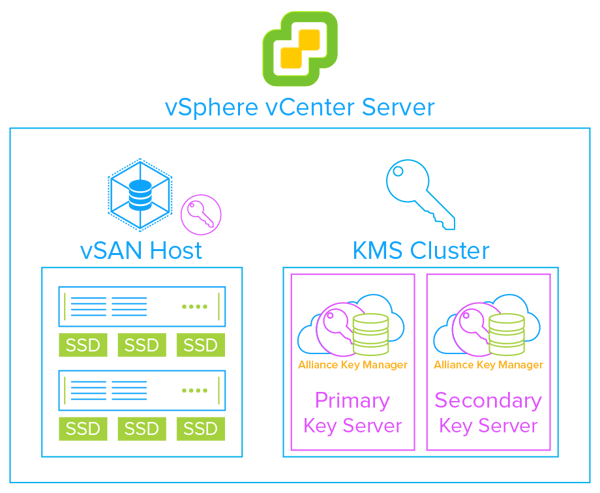
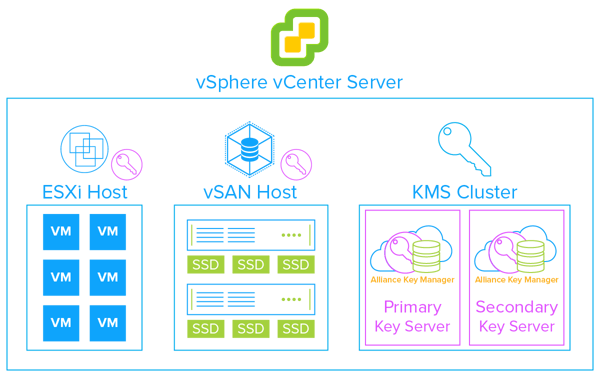
If you are an IT Support Provider or Managed Service Provider trying to help your customers with security, you are going to love our MSP Partner program. Affordable key management for VMware and the cloud, usage-based billing, and no upfront fees. You will be profitable from the first customer. More information here:
https://townsendsecurity.com/msp
Ransomware attacks can be devastating to an organization, but you have tools to protect yourself. Give us a call.
Patrick
References: