Data security compliance requirements and corporate security initiatives continue to drive the adoption of encryption and key management to protect private information - ranging from customer information to electronic protected health information (ePHI) to a company’s intellectual property (IP). Deploying encryption naturally means properly protecting encryption keys, which historically has been the biggest challenge that organizations face with their encryption strategy. As such, it is far too common to see businesses not properly storing their encryption keys - for example, keeping them in a database in the clear or even burned into their application’s code.
 Fortunately, encryption key management solutions are more affordable and easier than ever, however, not all solutions are created equal. Standards such as FIPS 140-2 remain, but what does that mean in a virtual environment? Additionally, we are seeing all the major cloud service providers (CSPs) offer encryption key management as a service, but there are several fundamental reasons enterprises are hesitant to adopt them.
Fortunately, encryption key management solutions are more affordable and easier than ever, however, not all solutions are created equal. Standards such as FIPS 140-2 remain, but what does that mean in a virtual environment? Additionally, we are seeing all the major cloud service providers (CSPs) offer encryption key management as a service, but there are several fundamental reasons enterprises are hesitant to adopt them.
I recently sat down with Patrick Townsend, Founder and CEO, to discuss the current state of encryption key management, databases/applications that natively provide encryption and key manager integrations, and questions to ask your key management vendor.
Hi Patrick. Let’s just take a minute and acknowledge how far encryption key management has come.
It is incredible how far encryption key management has come over the last 15 years. As I think back to when we started this journey, it was a very different environment. One of the motivating factors for us to get in the key management game was that key management systems used to be terribly expensive and complex - and usually involved a team of expensive consultants to deploy. Early on, I even had a key management system (KMS) vendor tell me that they didn’t want to do a deal under $10 million - and that just isn’t going to work for smaller companies. This just really influenced how we got started. Companies of all sizes deserve to have good encryption and key management as part of their defense in depth security strategy. I am very proud of our team for creating a key management solution that has been FIPS 140-2 validated and affordable to the small and medium sized enterprises who need to protect their employees and customers without having to pay for every database, connection, or encryption key. We have now passed the 10 year mark with Alliance Key Manager. While it was first introduced as a physical hardware security module (HSM), we have added VMware and cloud platforms (AWS and Microsoft Azure) - and starting at $4,800 is affordable to every customer. I am proud that we have played a part in making encryption key management affordable to businesses of all sizes.
Speaking of cost, could you imagine if deployments were still $10 million?
It really is incredible. If that were still the cost, small and medium sized businesses would be priced out of the market - and their data a lot more vulnerable. With that said, it still amazes me how much KMS vendors are still charging for some of their solutions. Recently we had a prospective customer forward us a quote from another KMS vendor and it was astonishing. The customer was trying to protect 12 Microsoft SQL Server databases and the quote was for $194,000! And that was just the start. As the customer adds additional databases in their environment, there is going to be more and more cost as they go forward. For the same hardware-based HSM solution, we would charge $36,000 for two HSMs and save the customer $158,000! Alternatively, we even could offer VMware or cloud instances that would have been even less expensive.
As a company, we are passionate about keeping a low and predictable total cost of ownership (TCO). You shouldn’t have to go back to your key management vendor every time you want to add a database or encrypt something in a new environment. This model of pricing can add up very quickly. We offer a simple pricing structure - license the KMS, pay annual maintenance, and use the key manager to protect as much data as you’d like. From my point of view, there is no justification for a pricing strategy that penalizes businesses for doing more security.
Aside from cost and ease of deployment, there really has been a growing awareness on the importance of key management. 10 years ago when you first started, small and medium sized businesses didn’t even know what key management was.
Certainly. Key management is the cornerstone of an encryption strategy. If you are doing encryption, you must protect encryption keys. In fact, key management is starting to show up in regulatory compliance requirements. For example, if you look at the California Consumer Privacy Act (CCPA), you will find proper key management called out as being core to protecting data. If you are not using key management, you are NOT adequately protecting your encryption keys and you lose some of the protections under the CCPA.
As businesses deploy modern key management solutions, they need to make sure the key manager has been FIPS 140-2 validated and is key management interoperability protocol (KMIP) compliant. The industry as a whole is still catching up to these standards. For example, with AWS KMS or Azure Key Vault, businesses do not have industry standards based interfaces for key management. Rather than using the KMIP standard, they are requiring customers to use their proprietary interface. Standards, like KMIP, are incredibly important when it comes to reducing your cost of encryption in the long run. Fortunately, we are seeing most major database and application vendors adopting the KMIP standard and natively supporting encryption, leaving the key management to the user.
Also, it is still the wild west out there in regards to some KMS vendors. I think people should avoid solutions that require external, third party hardware modules to back up the key manager. That is completely unnecessary. There are open source solutions that provide vaults that are not FIPS 140-2 compliant unless they are backed up by an HSM.
Again, key management is core to a security strategy and really has come a long way since the early days. It now takes a few minutes to get a KMS up and running, you don’t need outside consultants or someone to come on site, and most of the time doesn’t take any paid services!
You mentioned KMIP. It has been great to see more databases and applications adopt the standard.
That’s right. Encryption usually doesn’t require application changes anymore - it has become a non-technical exercise. KMIP has fundamentally changed the way businesses deploy encryption and key management. For example, we have seen databases like MongoDB and MySQL and VMware’s vSphere and vSAN support KMIP. Let’s take a look at MongoDB. MongoDB Enterprise includes 256-bit AES encryption built into the database. Knowing the importance of key management, they built in support for KMS vendors with the KMIP standard. Now their users can seamlessly encrypt data and easily manage the encryption keys separate from the data that they protect.
KMIP really has been a game changer for the key management industry and really underscores the importance of basing solutions on industry standards. Unfortunately, it isn’t everywhere - yet. Typically, KMIP is reserved for Enterprise versions of databases. With that said, there are still options for shops running “Standard” or “Community” versions.
There are. Chances are that these shops are running a version of VMware that supports vSphere and vSAN encryption. By deploying “Standard” versions of databases directly in vSAN, they can utilize the encryption and key management options already included in their VMware products. Furthermore, VMware has developed excellent guidance that is available on their website on how to install databases into an encrypted vSAN. If you are an Oracle customer, for example, and feel like you can’t afford the expense of upgrading to Oracle Enterprise with Advanced Security in order to get encryption, VMware has your back. By doing this, businesses can affordably meet regulatory compliance and protect their sensitive data. Same is true for other databases.
Let’s keep talking about compliance. Compliance has been a major driving force for organizations adopting encryption key management.
Yes. Businesses of all sizes and industries fall under a variety of compliance regulations. If you take credit cards, you fall under PCI DSS. If you are a covered entity in the medical segment you fall under HIPAA. California recently passed the California Consumer Privacy Act (CCPA) which has reach far beyond the borders of California. It is important to note that CCPA also requires proper key management. Storing encryption keys next to the secured data provides you no protection from data breach notification and class action lawsuits. You have to get key management right.
Regulations certainly are one major factor driving the uptake in encryption. Over time, we have seen regulations evolve and encryption keeps getting more embedded in these regulations and is recognized as a core part of a defense in depth strategy. With that said, compliance isn’t the only reason a company deploys encryption and key management. We regularly talk with customers concerned with reputation, protection of intellectual property (IP), or a host of other reasons.
For businesses who haven’t deployed encryption key management yet, what are some questions that they should ask vendors?
There are definitely some baseline qualifiers here. Look for a FIPS 140-2 validation. Has the solution ever been validated by the National Institute of Standard and Technology (NIST)? Some key management vendors out there will say they are compliant and unable to prove it because they have never received a formal validation. It is important to ask for their certificate number. Don’t accept a third-party letter saying that the solution is compliant. There is no substitute for a NIST validation. They aren’t cheap or easy, which is a major differentiator between the good and not-so-good key management vendors.
As discussed earlier, good key management systems will adopt the KMIP interface. You should easily be able to use your key management solution seamlessly with the growing number of databases and applications that support KMIP.
Who has administrative access to the keys? Do you have exclusive control or is access shared with a cloud service provider (CSP) or key management vendor? Most of the CSP key management offerings are in shared environments - both you and your CSP have access to your keys. Also a consideration, are you OK with CSP lock-in? Most businesses today are trying to achieve a cloud-neutral implementation and you don’t want your key management solution to defeat that effort.
I think that these are the topics that should be top of mind for businesses as they move through their cloud encryption strategy and think about key management.
Is there anything that you would like to share about Townsend Security’s Alliance Key Manager that you haven’t mentioned yet?
Alliance Key Manager comes along with a wide variety of client applications and SDKs - at no charge - to help you secure databases and applications like VMware, Microsoft SQL Server, MongoDB, MySQL and others. As I mentioned earlier, it is cost effective and affordable to organizations of all sizes. I think that our key manager is the most cost-effective, standards-based solution in the market. By offering the key manager on multiple platforms, which are all cross-compatible, businesses have a variety of options for their encryption strategy that are easy to deploy.
The last thing that I would like to point out is that our solution is very partner friendly. Alliance Key Manager is embedded in many ISV environments and products. We have flexible programs that allow our partners to get encryption right by embedding key management into their solution.
To hear this conversation in its entirety, download the podcast “State of Encryption Key Management - 2020” to hear Patrick Townsend, Founder and CEO, further discuss the latest trends and perspectives around encryption key management and how to better protect your data.

 MSP identifying and implementing top-notch business, security, and IT solutions
MSP identifying and implementing top-notch business, security, and IT solutions







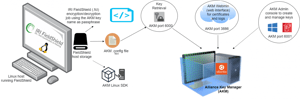 Innovative Routines International (IRI), Inc
Innovative Routines International (IRI), Inc
