What is vSAN Encryption?
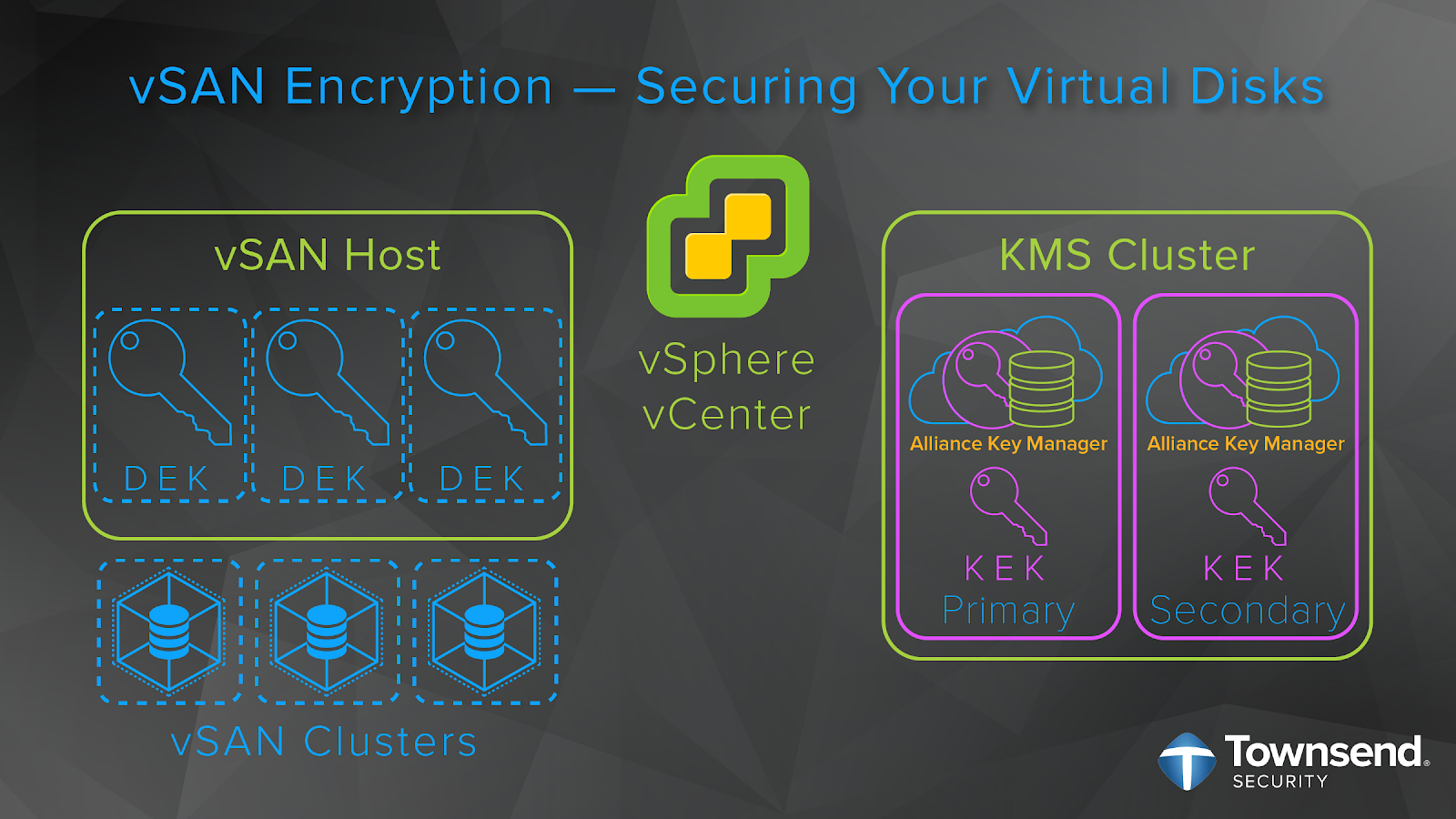
As of VMware vSAN 6.6, you can now encrypt your vSAN datastore. vSAN encryption protects your stored data in case a device is removed or hacked. vSAN encryption only requires the vCenter Server, a third-party Key Management Server (KMS), and ESXi hosts to work. It is standards based and KMIP compatible.
(Part one of this series deals with VM encryption. This post will cover vSAN encryption)
The Rise of Storage Area Networks
Nowadays, VMware vSAN provides hyper-converged storage for the enterprise business. As VMware puts it, “in addition to being incredibly simple to deploy and provision, Virtual SAN allows you to scale storage and compute resources, eliminating costly forklift upgrades.”
But, as most know, vSAN, first released in 2014, did not grow in a vacuum. Physical SANs started to gain traction in the early 2000’s as our need for data storage exploded. The SANS Institute, in 2002, highlighted these trends and the advantages that a SAN provided:
- Higher availability of systems and applications
- Costly IT purchases reduced
- Higher scalability of storage architecture
- Increased IT staff efficiency
- Higher ability to utilize the full value of a company’s information assets
 But even though a SAN brought these advantages to its user, it had one major limitation: Storage administrators were still tied to managing the data via where it physically lived, needing to pre-allocate storage on various servers.
But even though a SAN brought these advantages to its user, it had one major limitation: Storage administrators were still tied to managing the data via where it physically lived, needing to pre-allocate storage on various servers.
vSAN, however, overcomes the limitations of a purely physical SAN. Since vSAN is a software layer that sits on-top of the server, it allows for greater flexibility of your storage capacity. According to MicroAge:
“vSAN is software-defined storage that enables organizations to pool storage capabilities and automatically provision virtual machine storage. They can dynamically scale performance and storage capacity as needed and render underlying physical storage accessible to virtual machines through a policy-driven control pane. [O]rganizations use SANs to interconnect shared pools of storage devices to different servers. vSAN extends this local storage to a shareable storage in each server, enabling other servers to access data over the LAN without a traditional shared storage device.”
Another advantage of vSAN: greater (and much easier to implement) data security. With version 6.6 of vSAN, VMware introduced native encryption for your data-at-rest. vSAN encryption is baked right into vSAN and, as Jase McCarty of VMware puts it, “with a couple of clicks, it can be enabled or disabled for all items on the vSAN datastore, with no additional steps.”
This gives the enterprise business much greater control in how and when they secure their data. That said, let’s take a look at some additional advantages of using vSAN encryption.
Expert Weigh-in:
When it comes to database development and administration, there is often an emphasis on securing the data inside the database. Unfortunately, that’s not only one place that data resides. We all know that data exists outside the database engine. It’s important to take steps to protect your data no matter where it may lie. vSAN encryption allows for you take that extra step to protect your data-at-rest sitting in JSON, XML, or CSV files.
~Thomas LaRock, Head Geek, SolarWinds
The Advantages of vSAN Encryption

Minimizes Impact on Performance
With encryption there will always be a performance impact. It is just the nature of the beast. But with vSAN encryption, VMware reports:
- Minimal impact to CPU cycles while data is being encrypted.
- A 5-15% CPU penalty and no performance overhead. This overhead is representative of running vSAN with dedupe and compression turned on.
This is great news for those needing to encrypt large amounts of stored data. You can now protect your data and, in large part, maintain the integrity of your performance.
Streamlines Operations
As mentioned earlier, vSAN encryption is easy to configure and entire clusters can be encrypted with just a few clicks. There is zero guess-work with:
- No third-party encryption to install, configure, and maintain.
- No encryption at the hardware layer. Encryption at the hypervisor layer (vSAN encryption) has considerably less overhead than deploying encryption at the hardware layer.
Bring Your Own Key Manager
You can bring your preferred key manager to manage your encryption keys. Since vSAN encryption is KMIP 1.1 compatible, you are free to use a FIPS 140-2 compliant encryption key manager, like our Alliance Key Manager.
How Do I Enable vSAN Encryption?
The last and biggest advantage: vSAN encryption is easy to enable and use. This means that securing your sensitive data with AES encryption is not a time-intensive task. To prove the point, here is a quick guide to getting encryption up and running for your vSAN clusters:
- First, install and configure your key management server, or KMS, (such as our Alliance Key Manager) and add its network address and port information to the vCenter KMS Cluster.
- Then, you will need to set up a domain of trust between vCenter Server, your KMS, and your vSAN host.
- You will do this by exchanging administrative certificates between your KMS and vCenter Server to establish trust.
- Then, vCenter Server will pass the KMS connection data to the vSAN host.
- From there, the vSAN host will only request keys from that trusted KMS.
- The ESXi host generates internal keys to encrypt each disk, generating a new key for each disk. These are known as the data encryption keys, or DEKs.
- The vCenter Server then requests a key from the KMS. This key is used by the ESXi host as the key encryption key, or KEK.
- The ESXi host then uses the KEK to encrypt the DEK and only the encrypted DEK is stored locally on the disk.
- The KEK is safely stored separately from the data and DEK in the KMS.
- Additionally, the KMS also creates a host encryption key, or HEK, for encrypting core dumps. The HEK is managed within the KMS to ensure you can secure the core dump and manage who can access the data.
That’s it! VMware has made encrypting your data in vSAN both simple and secure.
Expert Weigh-in:
In traditional SAN infrastructures, layering key-based security and integrating with key managers has always been wrought with expense and complexity. It usually meant leveraging very few but very difficult to manage key management appliances which required very specialized skills. But with vSAN along with Alliance Key Manager, a lot of that complexity is removed—letting you focus on protecting your data instead of managing it.
~Christopher Kusek, vExpert and Tech Evangelist
Final Thoughts
Let’s face it, storage area networks are a target-rich environment for malicious actors. Whether it’s:
- Customer data
- Intellectual property
- Financial transactions
- Legal records
- Patient information
- And much, much more….
It all needs to be protected. Network administrators, though, face these challenges:
- They have little control over what gets put into storage.
- Sensitive data, many times, is stored by end users with little thought to encrypting it.
- There is a dizzying array of compliance regulations, internal security standards, and best practices that must be complied with.
vSAN encryption can help. With a few clicks in vSAN entire virtual disks can be encrypted. And with a FIPS 140-2 compliant encryption key manager, like Alliance Key Manager, the keys for your AES-NI encryption will be properly protected and full lifecycle managed.
If you are not protecting your data in vSAN, get started today! It’s not a matter of if your data will be hacked, but when.

