Still Have Questions About Meeting Compliance Requirements?
The question “Would You Pass An Audit?” was posed in our last blog and companion webinar series. We discussed compliance regulations and how protecting sensitive information was more than just a good security strategy. While the webinar title is directed at IBM i users, the content is really applicable to most all platforms! Hopefully you were able to watch the webinar resource provided (if not, you can request it HERE). After the webinar, we had a number of questions asked by attendees and answered by security expert Patrick Townsend. Here is a recap of that Q&A session:
Q: If I have my sensitive data stored off site with a hosting company or in the cloud am I responsible if they have a data breach?
A: The short answer is yes you are. When you have sensitive data and are moving it into a cloud solution you are still ultimately responsible for protecting that data. This can be confusing because cloud vendors make a lot of statements about encryption and compliance, however you are responsible for your overall data protection strategy.
When looking for a hosting vendor or to move applications outside of your environment, a part of the process should be assessing their ability to meet PCI or other compliance regulations. As part of your due diligence, ask for a QSA letter of attestation from a qualified QSA auditor to confirm the security of the infrastructure of that hosting company and that they are:
- Securing the data center to PCI standards
- Securing racks properly
- Placing proper controls and vulnerability scans in place for their own infrastructure
It is your responsibility to make sure your data security meets compliance regulations. Any loss will also be your responsibility, so it is worth the time to make sure you have a strong strategy in place and are using industry standard encryption and proper key management to protect your data wherever it resides.
Q: A vendor told me that tokenizing data will make us PCI compliant is this true?
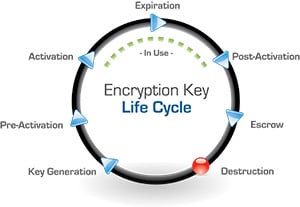
A: This is a more complex question to answer. Tokenization is a great technology and there has been a lot of work done in this field the past few years. Personally, I believe it can be done well and can help you meet compliance regulations. If you are planning to generate non-recoverable tokens (when the original data does not need to be recovered) using a separate token server, that can eliminate the need to store the original data in an encrypted format. Non-recoverable tokens can help minimize the impact of regulations such as HIPAA, PCI, HITECH , GLBA and individual state privacy laws by taking the server out of scope for compliance. However if you plan to recover the data and are consolidating sensitive information into the tokenization solution, you must make sure the tokenization solution itself is PCI compliant and using industry standard encryption such as AES when using recoverable tokens. The basic concept for tokenization is that you replace the data in your database with a token that has no value; however, sensitive data (for retrieval) has been transferred into the tokenization solution. Because all of this sensitive information has been consolidated into one place, it becomes even more of a high value target. Tokenization is very effective as long as you are using industry standard encryption within that solution and also using best practices for encryption key management. Make sure you are using a tokenization solution that integrates with a NIST validated and FIPS 140-2 compliant key management solution that will properly store your encryption keys on a designated hardware security module (HSM) and not in the same server as the pool of data.
Q: A vendor we are considering for key management advertises an integrated key management solution, would this be PCI compliant?
A: Only a QSA auditor can determine PCI compliance of vendor solutions, however being educated on industry best practices is very important.
Storing the key within the same server where the data is located is not a defensible practice, and security best practices recommend using an HSM to store encryption keys away from the data you are protecting. Best practices for encryption key management also recommend that you implement separation of duties and dual control. I highly recommend that you look for NIST validations and make sure the approach to encryption and key management has been done correctly.
To help you plan your data security strategy, we’ve created a great How-to-Guide on Encryption Best Practices and you can download your complimentary copy by clicking on the link below.