Questions and Answers on Encryption and Key Management Projects
VMware® is hands-down the virtualization choice of large and small organizations, and it is easy to see why. Not only is it a highly reliable and scalable platform, VMware also provides a complete set of tools you need to deploy, manage, monitor, and protect virtual machines.
Earlier this month, Paul Taylor with Security Insider - Podcast Edition spoke with our founder, Patrick Townsend about encrypting data on Microsoft SQL Server in VMware environments, steps to encrypting data on SQL Server (with and without TDE), as well as talk about Townsend Security’s Alliance Key Manager for VMware. Here are a few highlights (download the podcast for the whole conversation):
Paul Taylor: We’ve talked about the Townsend Security encryption and key management solutions for VMware. Today let’s put the focus on Microsoft SQL Server and encryption in the VMware customer environment. Can you give us an overview of how VMware customers can protect data in SQL Server databases?
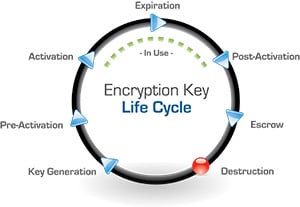
Patrick Townsend: Just to recap, we really need two things to get encryption right: A key management solution to protect the critical encryption keys, and an encryption solution for the SQL Server database. And they have to talk to each other.
For the first part, our Alliance Key Manager for VMware solution provides a fully functional, enterprise key management solution that protects SQL Server databases as well as other databases and other operating systems.
For encrypting SQL Server, our Alliance Key Manager solution comes with a full Microsoft SQL Server Extensible Key Management Provider. We call this Key Connection for SQL Server and it is one of the modules that our key management customers receive without paying additional license fees. Key Connection for SQL Server provides the encryption and integration with our key server to provide a complete, end-to-end solution for encrypting data in the SQL Server database.
Paul Taylor: Can you talk a little about how Microsoft enables encryption in SQL Server?
Patrick Townsend: If you are running SQL Server Enterprise Edition or higher, you have access to Microsoft’s automatic, full database encryption facility called Transparent Data Encryption, or TDE. You also have access to Microsoft’s automatic, column level encryption facility which Microsoft calls Cell Level Encryption. Both of these options, TDE and Cell Level Encryption, are implemented without any programming work at all. And both are fully supported by Alliance Key Manager and the Key Connection for SQL Server software from Townsend Security.
Paul Taylor: What about Microsoft customers who aren’t using the Enterprise Edition of SQL Server? Can they encrypt their data with the Townsend Security solution?
Patrick Townsend: With SQL Server Standard and Web Editions we provide two paths to encrypt data. The first is to use SQL Views and Triggers along with our .NET DLL to provide automatic encryption without any changes to applications. And the second path is to modify your C# or Java applications to use our .NET DLL to perform encryption at the application level.
Both approaches leverage our Microsoft .NET DLLs to perform encryption with integrated key management. Both are very simple to implement. And there are no additional license fees to deploy and use our Microsoft .NET DLLs to accomplish this.
Paul Taylor: So, walk me through the steps for encrypting data in my SQL Server Enterprise Edition database. How difficult is it?
Patrick Townsend: Encrypting data in Enterprise SQL Server is really very easy. The first step is to install our Alliance Key Manager for VMware solution. It launches like any other virtual machine using the normal VMware applications and you can have a key management solution up and running very quickly.
The second step is to install the Key Connection for SQL Server application on the virtual machine running SQL Server in Windows. This is a normal install process with an MSI file. You answer some questions, install a certificate and private key in the Windows Certificate Store, and run a handful of commands to start SQL Server TDE encryption or Cell Level Encryption. You also restart the log file to be sure that it is encrypted as well. That’s about it.
Of course, you will want to follow the instructions on how to set up a high availability key server, and point your Key Connection for SQL Server configuration to it as failover. That is a normal configuration process and also very easy to do. We find that VMware customers can deploy SQL Server encryption very quickly.
Paul and Patrick also cover which versions of SQL Server are supported, the availability of Alliance Key Manager in other platforms (hint: it’s quite versatile), and our 30-day evaluation program (you can do a full proof-of-concept in your own environment at no charge). Be sure to download the podcast to hear the rest of their conversation: