What is VMware’s vSphere Encryption?
VMware’s vSphere encryption, first introduced in vSphere 6.5, enables the encryption of virtual machines (VMs) and vSAN. vSphere’s encryption protects your existing VMs, new VMs, vSAN clusters, as well as associated files. It is relatively easy to set up and with the use of a compliant key management server—secure.
(Part one of this series deals with VM encryption. Part two will cover vSAN encryption)
A Unified Way to Encrypt VMs
“Dance like nobody’s watching. Encrypt like everyone is.”
~Werner Vogels, CTO at Amazon.com
Data is a bedrock asset for today’s enterprise business. Its value is too great to ignore. Data security, then, is mission critical for those looking to maintain brand integrity, intellectual property confidentiality, and customer trust.
VMware vSphere 6.5 gave its users powerful data security tools; among them AES-NI encryption. The reason this is great news: instead of an ad-hoc approach to encrypting sensitive data where individual sources of encryption are found for each type of database or application, you can now encrypt directly in VMware’s hypervisor creating a unified source for encrypting and managing that encryption. And through their KMIP interface, managing your encryption keys is pretty painless. But more on that later.
vSphere encryption, then, allows the enterprise business to uniformly manage their encryption for both VMs and vSAN and ensure that all sensitive data within VMware is secured. This enables companies to create an encryption strategy for their sensitive data. Let’s look at some of the main advantages, specifically VM encryption, that vSphere encryption provides.
Expert Weigh-in:
The huge benefit of vSphere Encryption is the fact that data is encrypted when it leaves its source. This results in data traveling encrypted to its destination, allowing for the highest level of security, all while maintaining simplicity in terms of management and configuration.
~Duncan Epping, Chief Technologist HCI, VMware
Expert Weigh-in:
A major advantage of VM Encryption is that it is Guest OS agnostic. Whether the virtual machine is Windows, Linux or any of the other operating systems supported in vSphere, the encryption is the same. There’s no change to the guest OS and no “in guest” monitoring or configuration. Additionally, reporting on which virtual machines are encrypted or not is just one line of PowerCLI!
~Mike Foley, Staff Technical Marketing Architect - vSphere Security
The Advantages of Using VM Encryption
With VMware vSphere 6.5 and up, you are able to encrypt individual VMs. The main difference between VMware encryption and other encryption methods is ease
 of management. As VMware puts it, because “VMs are treated as objects that can have a policy applied to them, there is no need to manage them individually.”
of management. As VMware puts it, because “VMs are treated as objects that can have a policy applied to them, there is no need to manage them individually.”
Here are some of the advantages that this brings:
- Encryption is configured and managed at the hypervisor level, not within an individual VM.
- vSphere encryption is agnostic in regards to what is stored within the VM.
- There are not multiple encryption products for each guest OS, database, or application.
- Encryption is policy based. Applying it, then, can be done to as many or few VMs that you want.
- You can bring your prefered key manager to manage your encryption keys. Since vSphere encryption is KMIP 1.1 compatible, you are free to use a FIPS 140-2 compliant encryption key manager, like Alliance Key Manager.
Expert Weigh-in:
One thing few people think about with encryption is disaster recovery. Because of the reliance on an external KMS, you can place replicating Key Managers in various locations. vCenter will see them as a “KMS Cluster”. Should your primary site go down and you need to recover encrypted VM’s it’s as simple as connecting a new vCenter to the KMS cluster and adding the VMs to the inventory. The impact of IT operations is minimal.
~Mike Foley, Staff Technical Marketing Architect - vSphere Security
Expert Weigh-in:
Policy Based encryption and Managed Encryption keys means the difference between an organization protecting their information and exposing their information. Removing the chance of end-users to not-encrypt information means the Business can have assurances they can take to the bank, which is essential in a world of compliance, GDPR, and not to mention security risks or exposure.
~Christopher Kusek, vExpert and Tech Evangelist
Now that we know some of the advantages of using VM encryption, let’s looks what is (and is not) encrypted. Why? VMware did a great job making sure all sensitive information can be secured. The list below will go to illustrate that.
What Is/Is Not Encrypted
According to VMware, here are the items that can be encrypted (and those that can’t) with vSphere’s VM encryption:
What can be encrypted:
- VM files
- Note: Most VM files can be encrypted. This set of files can include the NVRAM, VSWP, and VMSN files. If you use the vSphere Web Client to create an encrypted VM, all virtual disks will be encrypted as well.
- Virtual disk files
- Note: Data in an encrypted VMDK file is never written in plaintext to storage or a physical disk, and is never transmitted in plaintext. The VMDK descriptor file, however, is not encrypted and contains a key ID for the key encryption key (KEK) as well as the encrypted data encryption keys (DEKs).
- Host core dump files
- Note: When you enable encryption mode on an ESXi host the core dump is always encrypted.
What is not encrypted (and why):
- Log files
- Why: these are not encrypted because they contain no sensitive data.
- VM configuration files
- Why: the VM configuration information, stored in the VMX and VMSD files, contains no sensitive data.
- Virtual disk descriptor files
- Why: the descriptor file is omitted from encryption/decryption functions to support disk management without a need for an encryption key.
Expert Weigh-in:
I like vSphere encryption because there’s nothing in the guest OS or at the user-level that might go wrong. vSphere encryption encrypts what needs to be encrypted - your company’s data - that’s stored inside the VM disk.
~David Davis, vExpert and vSphere video training author at Pluralsight.com
How it Works
Now that we know some of the advantages of VM encryption and what can and cannot be encrypted; here is the last reason to use vSphere to create a unified encryption strategy—it is easy to set up. Here is a quick video showing how easy it is.
Here are those steps for those that would like to just read it:
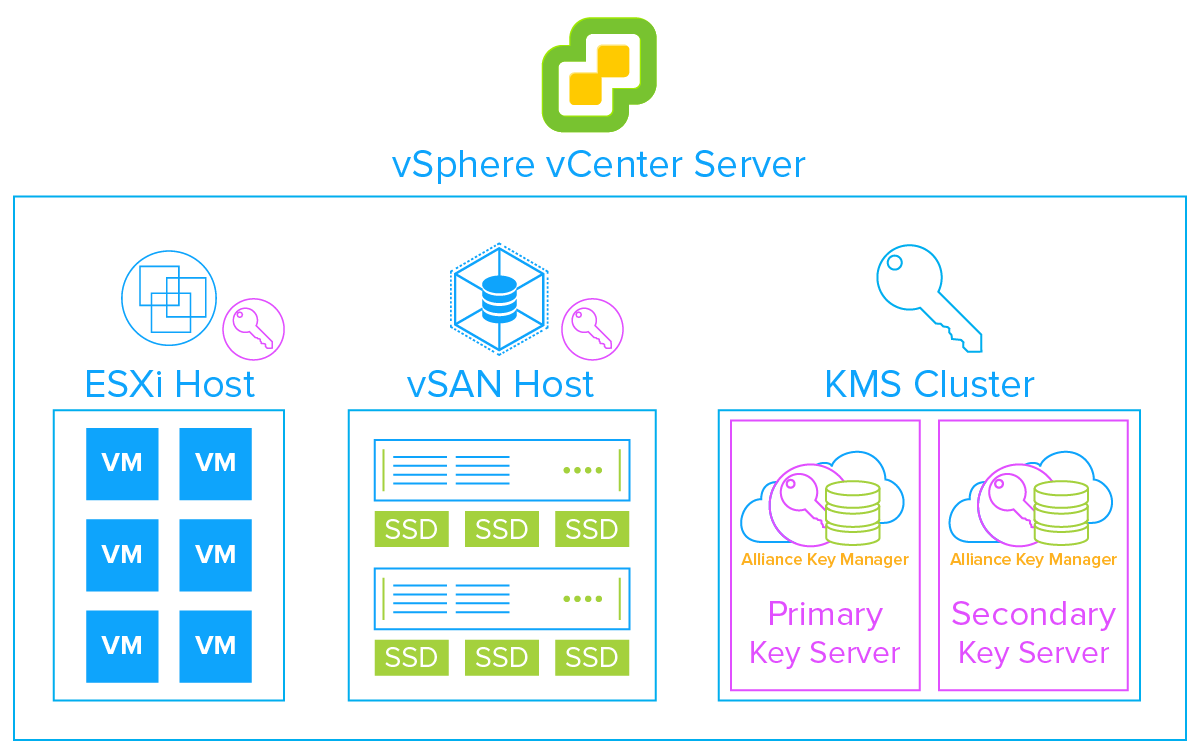
- First, install and configure your KMIP compliant key management server, such as our Alliance Key Manager, and register it to the vSphere KMS Cluster.
- Next, you must set up the key management server (KMS) cluster.
- When you add a KMS cluster, vCenter will prompt you to make it the default. vCenter will provision the encryption keys from the cluster you designate as the default.
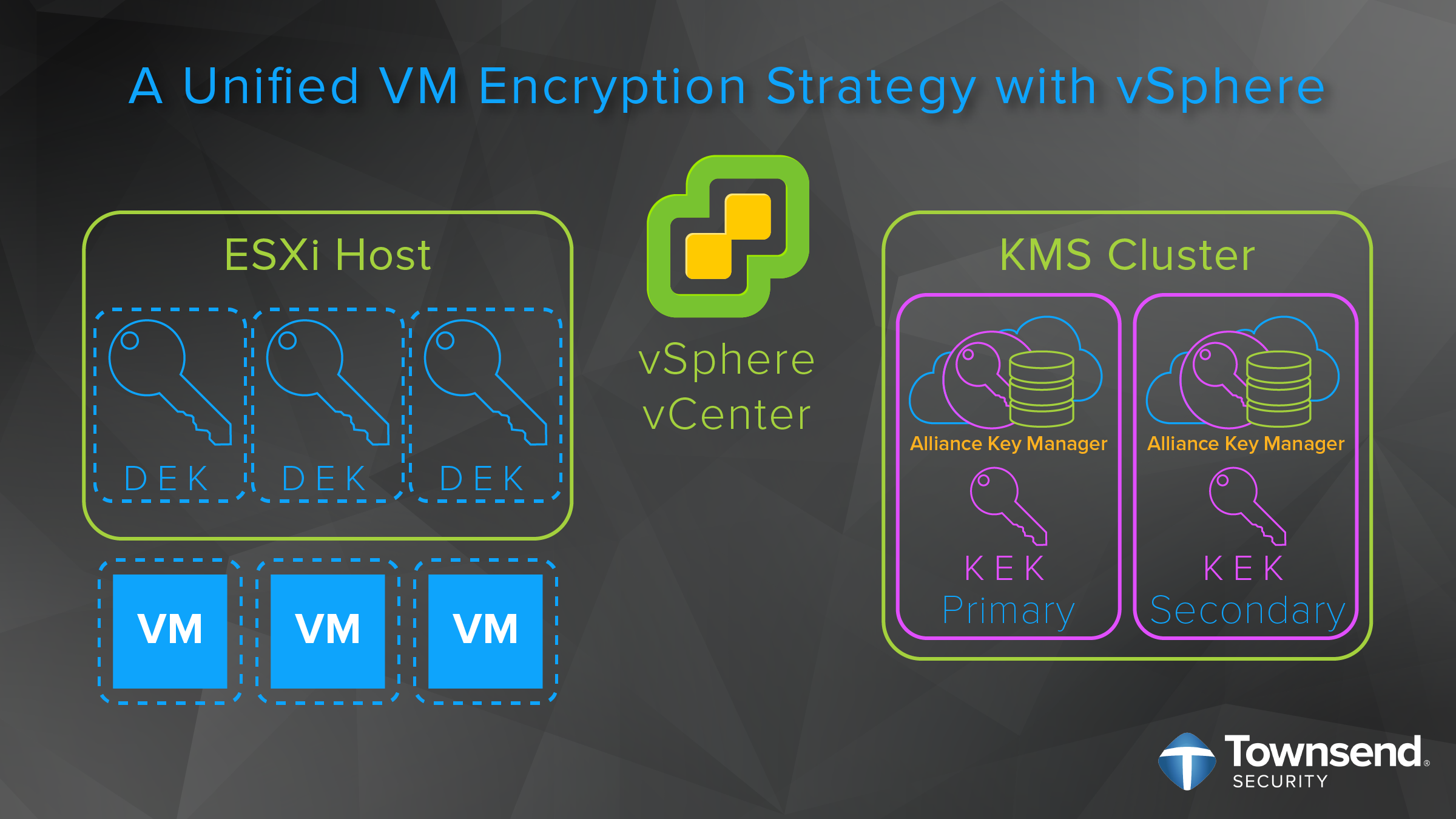
- Then, when encrypting, the ESXi host generates internal 256-bit (XTS-AES-256) DEKs to encrypt the VMs, files, and disks.
- The vCenter Server then requests a key from Alliance Key Manager. This key is used as the KEK.
- ESXi then uses the KEK to encrypt the DEK and only the encrypted DEK is stored locally on the disk along with the KEK ID.
- The KEK is safely stored in Alliance Key Manager. ESXi never stores the KEK on disk. Instead, vCenter Server stores the KEK ID for future reference. This way, your encrypted data stays safe even if you lose a backup or a hacker accesses your VMware environment.
Expert Weigh-in:
vSphere encryption makes securing your data easier than I think most of us thought possible. With vSphere encryption all you do is right-click on a VM and apply the encryption storage policy. Boom! Encryption is done!
~David Davis, vExpert and vSphere video training author at Pluralsight.com
It really is that easy. Not only can govern your encryption at the hypervisor layer, deploy standards based AES encryption on a per VM basis (allowing you to secure only those workloads that require it), but you can do so quickly. It is a great encryption option for any business.
Final Thoughts
VMware vSphere VM encryption creates a unified strategy for protecting your sensitive data within vSphere by using the hypervisor to perform the encryption. This means that you do not need to first consider what is in the VM (guest OS, specific databases, etc.) in order to encrypt it. According to VMware, this yields the following benefits:
- No modification to OSs within VMs
- No changes needed to existing applications
- No specialized hardware or infrastructure required
- Policy-based enforcement that is supported by vSphere
All this and more means that it is easier than ever to secure your company’s sensitive data. Once you have configured your vSphere vCenter Server to enable encryption, simply choose which VMs you want to encrypt and your data is secured. It’s that easy.
According to RiskBased Security, for the first half of 2019, over 3,800 breaches were reported, breaching over 4.1 billion records. When you compare that to the first half of 2018, “the number of reported breaches was up 54% and the number of exposed records was up 52%.” With the pace of breaches only accelerating, the time to create a unified encryption strategy for your sensitive data is now.

 Manager through their partnership with Coalfire, and then achieved certified status of our key manager with VMware encrypted VMs and vSAN. Now we are working towards an enhanced marketplace presence where our customers can actually purchase our key manager through the VMware marketplace portal.
Manager through their partnership with Coalfire, and then achieved certified status of our key manager with VMware encrypted VMs and vSAN. Now we are working towards an enhanced marketplace presence where our customers can actually purchase our key manager through the VMware marketplace portal.